Unveiling the Power of Artificial Intelligence in Origin Detection and Impact Analysis

In a rapidly evolving technological landscape, artificial intelligence (AI) is revolutionizing numerous industries, including the field of origin detection and impact analysis. This cutting-edge technology empowers organizations to identify the origins of malicious activities and gauge their potential impact with unprecedented accuracy and speed.
4.2 out of 5
| Language | : | English |
| File size | : | 38546 KB |
| Screen Reader | : | Supported |
| Print length | : | 452 pages |
Origin Detection: Unraveling the Source of Threats
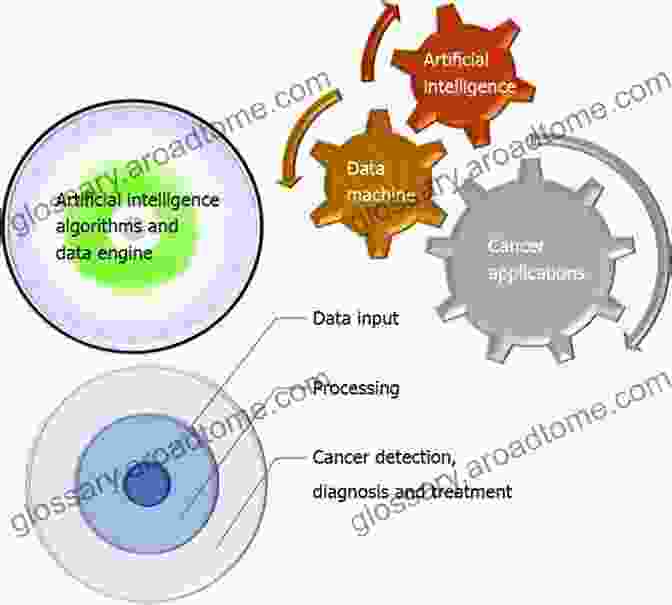
AI-powered origin detection systems analyze vast amounts of data across multiple sources, including network traffic, endpoint devices, and cloud platforms, to pinpoint the root cause of cybersecurity incidents. By leveraging machine learning algorithms, these systems can detect anomalies and identify patterns indicating malicious activities. This comprehensive analysis enables organizations to respond quickly to threats, mitigating potential damages.
Benefits of AI-Powered Origin Detection
- Enhanced Detection Accuracy: AI algorithms continuously learn and adapt, improving the accuracy of threat detection over time.
- Rapid Response: AI systems can detect threats in near real-time, enabling organizations to respond promptly and effectively.
- Proactive Identification: AI algorithms can identify potential threats before they manifest, allowing organizations to take preventive measures.
Impact Analysis: Quantifying the Severity of Threats
Once the origin of a threat has been identified, AI can also assist in assessing its potential impact. Impact analysis engines leverage threat intelligence, historical data, and industry best practices to estimate the likelihood and severity of damage. This helps organizations prioritize resources and allocate them where they are most needed.
Benefits of AI-Powered Impact Analysis
- Informed Decision-Making: AI-generated impact assessments provide organizations with actionable insights to guide their response strategies.
- Resource Optimization: By quantifying the impact of threats, organizations can allocate their limited resources effectively.
li>Improved Business Continuity: AI-powered impact analysis assists organizations in developing robust business continuity plans, ensuring minimal disruption in the event of a security breach.
Case Studies and Real-World Applications
The benefits of AI-powered origin detection and impact analysis have been demonstrated in numerous real-world scenarios:
- Financial Institution: An AI-driven origin detection system identified a phishing campaign targeting customer accounts, allowing the institution to swiftly block the attack and protect its customers' sensitive financial data.
- Healthcare Provider: An AI-powered impact analysis engine estimated the potential impact of a ransomware attack, enabling the healthcare provider to prioritize the recovery of critical patient records and minimize disruption to patient care.
- Government Agency: An AI-enabled origin detection system detected an advanced persistent threat (APT) targeting sensitive national security information, leading to the identification and neutralization of the attackers.
Origin detection and impact analysis using artificial intelligence offer organizations an invaluable tool for combating cybersecurity threats. By leveraging the power of AI, organizations can enhance their ability to identify threats, gauge their impact, and respond promptly and effectively. This comprehensive approach ensures business continuity, protects critical assets, and fosters a more secure digital environment.
As technology continues to advance, AI-powered origin detection and impact analysis will play an increasingly crucial role in safeguarding organizations against the evolving threatscape. Investing in these technologies is an essential step towards ensuring a secure and resilient digital future.
4.2 out of 5
| Language | : | English |
| File size | : | 38546 KB |
| Screen Reader | : | Supported |
| Print length | : | 452 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Amelia Hutchins
Amelia Hutchins Gareth Branwyn
Gareth Branwyn Gabe Henry
Gabe Henry Sandra Sealy
Sandra Sealy Gary Jonas
Gary Jonas Gamaliel Anguiano
Gamaliel Anguiano Geir Anton Johansen
Geir Anton Johansen Liam Garden
Liam Garden Maya Angelou
Maya Angelou Gareth St John Thomas
Gareth St John Thomas Steve Slocum
Steve Slocum Shamim Tejani
Shamim Tejani Gamal Elfouly
Gamal Elfouly George Pottinger
George Pottinger Gene Derumor
Gene Derumor Frederick Dodson
Frederick Dodson George Ho
George Ho Matthew P Binkewicz
Matthew P Binkewicz Gabriel Campisi
Gabriel Campisi Gary Bell
Gary Bell
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Arthur C. ClarkeUnlock Your Potential with Psychotherapy Essentials To Go: The Ultimate Guide...
Arthur C. ClarkeUnlock Your Potential with Psychotherapy Essentials To Go: The Ultimate Guide...
 Yasunari KawabataAn Introduction to Geotechnical Considerations in Highway Pavement Design
Yasunari KawabataAn Introduction to Geotechnical Considerations in Highway Pavement Design
 Rudyard KiplingUnveiling the Essential Guide for Reliability-Focused Operators: What Every...
Rudyard KiplingUnveiling the Essential Guide for Reliability-Focused Operators: What Every... Allan JamesFollow ·17.5k
Allan JamesFollow ·17.5k Rick NelsonFollow ·9.9k
Rick NelsonFollow ·9.9k Vladimir NabokovFollow ·15.7k
Vladimir NabokovFollow ·15.7k Don ColemanFollow ·3.6k
Don ColemanFollow ·3.6k Gordon CoxFollow ·6.7k
Gordon CoxFollow ·6.7k Al FosterFollow ·11.2k
Al FosterFollow ·11.2k Aubrey BlairFollow ·11.1k
Aubrey BlairFollow ·11.1k Daniel KnightFollow ·12.7k
Daniel KnightFollow ·12.7k
 Chinua Achebe
Chinua AchebeLetters to My Bipolar Self: A Journey of Hope, Healing,...
Bipolar disFree...
 John Parker
John ParkerLearning to Breathe from the Breath Itself: A...
In the whirlwind of modern life, finding...

 Beau Carter
Beau CarterExperiences In Psychoanalysis: A Journey into the...
Are you fascinated by the...
 George Hayes
George HayesExperiences Of The Neurological Condition Dystonia
Navigating the Labyrinth of a Complex...
 Jerome Powell
Jerome PowellOver 50 Keto Meal Prep Recipes: Your Essential Guide to...
Welcome to the world...
4.2 out of 5
| Language | : | English |
| File size | : | 38546 KB |
| Screen Reader | : | Supported |
| Print length | : | 452 pages |